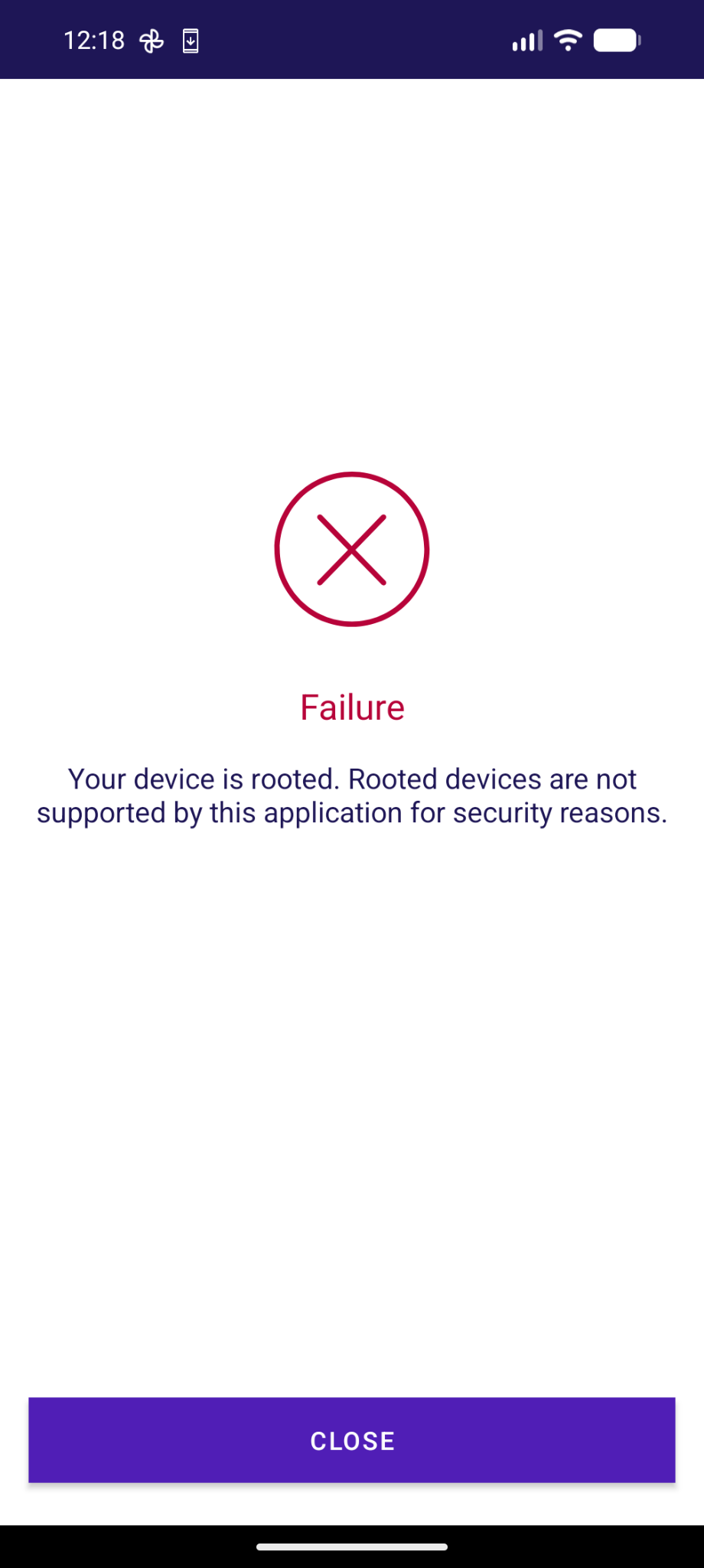
😡 So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht.
-
 So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...
So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...Gestern an der interessanten Konferenz TRANSFORM zu Digital Public Infrastructure haben Bundeskanzlei, BAG-Vertreter:innen betont wie wichtig es sei, dass der Staat wie bei der Eisenbahn eine digitale hoheitliche Infrastruktur schafft (auch wenn sie von Privaten gebaut wird).
Digital ist das natürlich etwas schwieriger zu übersetzen, wegen Datenhaltung, Hardware, Software und technologischen Abhängigkeiten. Dennoch: der Big Tech-Zwang bei der Agov Access App ist eine absolute Frechheit. Nur für iOs und Android.
Zwar gelobt die Bundeskanzlei Besserung und will diese verfügbar machen für alternative Betriebssysteme. Ob die eID am 1.12.2026 für Nicht-iOS/Nicht-Android-Usern zur Verfügung stehen wird, das steht noch in den Sternen.
Es kann nicht sein dass man von digitaler öffentlicher Infrastruktur redet, jedoch alle Einwohner:innen dieses Landes nötigt das Big Tech-Duopol (von den man sich ja ironischerweise allgemein emanzipieren will) zu installieren.
@GrapheneOS One more app to add for your "Wall of Shame".
Mein Text dazu folgt am Montag.
(morgen kommt was zu Überwachung und VÜPF 2.0, kleiner Teaser;))
Hihi, bin gespannt, ob ich so etwas auf ubuntu touch mit Waydroid hinkriege. Bin am Pröbeln. Threema hatte ich schon malzum Laufen gebracht.
-
Das ist unschön, aber immerhin kannst du dich auf AGOV anstatt mit der App auch mit einem Sicherheitsschlüssel einloggen. Der Token2 PIN+ Mini-C FIDO2 Key hat mich keine 24 Franken gekostet (inklusive Versand) und hat mit fido2-manage gar ein FOSS Management Tool, das auf Linux läuft und bei mir ohne Weiteres funktionierte.
@rolandlo @adfichter @GrapheneOS Das war bei mir dieselbe Erfahrung, FIDO2-Stick lief entgegen der Erwartung einwandfrei und ohne Zusatzaufwand unter Linux und wird nächstes Jahr zur Steuererklärung wieder rausgekramt. Es kann aber trotzdem nicht sein, dass eine ältere AGOV-Version unter GrapheneOS funktioniert, aber neuere nicht mehr.
-
@adfichter @GrapheneOS Wenn man Native Code Debugging unter Exploit Protection deaktiviert (und einmal neustartet) geht die AGOV-App. Aber trotzdem unsinnig, dass man die Sicherheit des ganzes Systems reduzieren muss, nur um die eine App zum Laufen zu bringen.
Korrektur: Die richtige Einstellung, die man deaktivieren muss, heisst "Secure App Spawning", ebenfalls unter Exploit Protection
@flozo @adfichter Die Einstellung kann man auch pro App ändern. Das muss man nicht systemweit machen. Aber ob es den gleichen Effekt hat, kann ich nicht sagen.
-
Bei e/OS/ übrigens auch, da funktioniert sogar die UBS-App. Nur bei iodéOS konnte ich diese nicht zum Laufen bringen.
@unaegeli @jonasgraphie @f @adfichter @GrapheneOS
Mich warnt die UBS-App, dass sie bald nicht mehr funktionieren wird auf meinem GrapheneOS mit gelocktem Bootloader.
-
@flozo @adfichter Die Einstellung kann man auch pro App ändern. Das muss man nicht systemweit machen. Aber ob es den gleichen Effekt hat, kann ich nicht sagen.
@truls46 @adfichter Du hast Recht, ich habe mich in den Einstellungen vertan: was man deaktivieren muss, ist Secure App Spawning. Das ist systemweit und bringt die AGOV-App zum Laufen. Sorry für die Verwechslung!
-
 So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...
So sieht die Agov Access App bei mir aus, die man in der Schweiz für digitale Behördengänge braucht. Und ja, es macht mich hässig...Gestern an der interessanten Konferenz TRANSFORM zu Digital Public Infrastructure haben Bundeskanzlei, BAG-Vertreter:innen betont wie wichtig es sei, dass der Staat wie bei der Eisenbahn eine digitale hoheitliche Infrastruktur schafft (auch wenn sie von Privaten gebaut wird).
Digital ist das natürlich etwas schwieriger zu übersetzen, wegen Datenhaltung, Hardware, Software und technologischen Abhängigkeiten. Dennoch: der Big Tech-Zwang bei der Agov Access App ist eine absolute Frechheit. Nur für iOs und Android.
Zwar gelobt die Bundeskanzlei Besserung und will diese verfügbar machen für alternative Betriebssysteme. Ob die eID am 1.12.2026 für Nicht-iOS/Nicht-Android-Usern zur Verfügung stehen wird, das steht noch in den Sternen.
Es kann nicht sein dass man von digitaler öffentlicher Infrastruktur redet, jedoch alle Einwohner:innen dieses Landes nötigt das Big Tech-Duopol (von den man sich ja ironischerweise allgemein emanzipieren will) zu installieren.
@GrapheneOS One more app to add for your "Wall of Shame".
Mein Text dazu folgt am Montag.
(morgen kommt was zu Überwachung und VÜPF 2.0, kleiner Teaser;))
@adfichter This app works on GrapheneOS with the exploit protection compatibility mode disabled and secure spawning disabled. The app does incorrect anti-tampering checks which are incompatible with our secure spawning feature due to it causing small differences in the address space and properties checked by their anti-tampering. The exploit protection compatibility mode has to force enable secure spawning to disable hardened_malloc and the 48-bit address space so it has to be disabled.
-
@adfichter This app works on GrapheneOS with the exploit protection compatibility mode disabled and secure spawning disabled. The app does incorrect anti-tampering checks which are incompatible with our secure spawning feature due to it causing small differences in the address space and properties checked by their anti-tampering. The exploit protection compatibility mode has to force enable secure spawning to disable hardened_malloc and the 48-bit address space so it has to be disabled.
@adfichter Disabling secure spawning reverts to the standard Android Zygote-based spawning model where apps start as clones of the Zygote address space and memory. The Zygote spawning model reduces security by sharing the same state for probabilistic exploit protections including hardware memory tagging (MTE), ASLR, heap canaries, heap randomization and more. Android has a workaround to avoid weakening the security of stack canaries (SSP) but the rest can't really be worked around for it.
-
@adfichter Disabling secure spawning reverts to the standard Android Zygote-based spawning model where apps start as clones of the Zygote address space and memory. The Zygote spawning model reduces security by sharing the same state for probabilistic exploit protections including hardware memory tagging (MTE), ASLR, heap canaries, heap randomization and more. Android has a workaround to avoid weakening the security of stack canaries (SSP) but the rest can't really be worked around for it.
@adfichter Our secure spawning feature was never expected to cause any compatibility issues. We aren't aware of any legitimate compatibility issues as opposed to apps doing incorrect anti-tampering checks which make incorrect assumptions about non-stable OS implementation details. Due to these incorrect checks, these apps frequently break with new major Android OS releases. They often don't address it during Android's Developer Preview or Beta testing but rather weeks after the Stable release.
-
@adfichter Our secure spawning feature was never expected to cause any compatibility issues. We aren't aware of any legitimate compatibility issues as opposed to apps doing incorrect anti-tampering checks which make incorrect assumptions about non-stable OS implementation details. Due to these incorrect checks, these apps frequently break with new major Android OS releases. They often don't address it during Android's Developer Preview or Beta testing but rather weeks after the Stable release.
@adfichter Various banking apps used to ban GrapheneOS because the secure spawning feature had a different initial Java call stack. We addressed this by making the call stack match for secure spawning which fixed most of the compatibility issues. There are still minor differences which are possible for apps to detect if they're checking implementation details such as low-level system properties, the address space layout or how much is initially preloaded. We plan to work around all of that too.
-
@adfichter Various banking apps used to ban GrapheneOS because the secure spawning feature had a different initial Java call stack. We addressed this by making the call stack match for secure spawning which fixed most of the compatibility issues. There are still minor differences which are possible for apps to detect if they're checking implementation details such as low-level system properties, the address space layout or how much is initially preloaded. We plan to work around all of that too.
@adfichter For now, you can disable secure spawning if you need to use this app on GrapheneOS. Turning it off disables it for every system process implemented with app_process including system_server and various privileged components such as the main Bluetooth process. We could provide a more granular way to disable it. We didn't anticipate anti-tampering checks causing compatibility issues and the toggle was only added as a way to test memory usage and app spawning time without it enabled.
-
@adfichter For now, you can disable secure spawning if you need to use this app on GrapheneOS. Turning it off disables it for every system process implemented with app_process including system_server and various privileged components such as the main Bluetooth process. We could provide a more granular way to disable it. We didn't anticipate anti-tampering checks causing compatibility issues and the toggle was only added as a way to test memory usage and app spawning time without it enabled.
@adfichter The anti-tampering checks done by these are inherently insecure and most are incorrect which leads to compatibility issues with future Android versions, GrapheneOS and even OEM Android forks. The reason we had to adjust the initial call stack for secure spawning to match the standard one is because some apps insecurely try to detect tampering via method hooking by checking the call stack. We can make a similar change for their low-level checks of the data in certain memory blocks too.
-
@cxor its ON and it doesn't work... @GrapheneOS
@adfichter @cxor The app will work if you turn off exploit protection compatibility mode and disable secure spawning. We don't recommend doing this because secure spawning is an important security feature and we mainly provided the toggle for testing memory usage and cold start app spawning time with vs. without it. We've considered moving the toggle to developer options and making it only last 1 reboot but we've kept it around due to these rare compatibility issues. See https://grapheneos.social/@GrapheneOS/116528377935838679.
-
@jonasgraphie @adfichter @GrapheneOS
Ja, daher genau richtig...Aufklärung überall und wo es nur geht.
@andree4live It's caused by incorrect anti-tampering checks and can be worked around by disabling an important security feature added by GrapheneOS (secure app spawning), which we don't recommend. It's possible to use this app on GrapheneOS already but we plan to come up with a built-in workaround which avoids needing to turn off secure spawning. See https://grapheneos.social/@GrapheneOS/116528377935838679.
-
V.a. ist es eine dreiste Lüge dass das Gerät gerooted sei.
@jonasgraphie It's caused by incorrect anti-tampering checks and can be worked around by disabling an important security feature added by GrapheneOS (secure app spawning), which we don't recommend. It's possible to use this app on GrapheneOS already but we plan to come up with a built-in workaround which avoids needing to turn off secure spawning. See https://grapheneos.social/@GrapheneOS/116528377935838679.
-
@truls46 @adfichter Du hast Recht, ich habe mich in den Einstellungen vertan: was man deaktivieren muss, ist Secure App Spawning. Das ist systemweit und bringt die AGOV-App zum Laufen. Sorry für die Verwechslung!
@flozo @truls46 @adfichter The app has incorrect anti-tampering checks and can be used on GrapheneOS with secure spawning disabled, which we don't recommend. Secure spawning is an important security protection improving app and OS security. The per-app exploit protection toggle needs to be disabled rather than enabled since it depends on secure spawning. We've already worked around most of these anti-tampering checks and plan to work around the rest.
See https://grapheneos.social/@GrapheneOS/116528377935838679 for details.
-
@f @jonasgraphie @adfichter GrapheneOS uses a locked bootloader and has full support for verified boot. We expand verified boot to covering more than it does for standard Android. GrapheneOS adds many important privacy and security protections. It's far more secure than any OS permitted by the Play Integrity API or incorrect checks like this. The security feature this app is detects as tampering can be disabled to use it on GrapheneOS but we recommend leaving it on.
GrapheneOS (@GrapheneOS@grapheneos.social)
@adfichter@infosec.exchange This app works on GrapheneOS with the exploit protection compatibility mode disabled and secure spawning disabled. The app does incorrect anti-tampering checks which are incompatible with our secure spawning feature due to it causing small differences in the address space and properties checked by their anti-tampering. The exploit protection compatibility mode has to force enable secure spawning to disable hardened_malloc and the 48-bit address space so it has to be disabled.

GrapheneOS Mastodon (grapheneos.social)
-
Bei e/OS/ übrigens auch, da funktioniert sogar die UBS-App. Nur bei iodéOS konnte ich diese nicht zum Laufen bringen.
@unaegeli @jonasgraphie @f @adfichter This app works fine on GrapheneOS with the important secure spawning feature it adds disabled. The app wrongly detects the security protection as tampering due to incorrectly written anti-tampering checks which make bad assumptions about internal implementation details they can detect by scanning properties and memory. See https://grapheneos.social/@GrapheneOS/116528377935838679 for details. We don't recommend turning off this important security protection added by GrapheneOS though.
-
@unaegeli @jonasgraphie @f @adfichter This app works fine on GrapheneOS with the important secure spawning feature it adds disabled. The app wrongly detects the security protection as tampering due to incorrectly written anti-tampering checks which make bad assumptions about internal implementation details they can detect by scanning properties and memory. See https://grapheneos.social/@GrapheneOS/116528377935838679 for details. We don't recommend turning off this important security protection added by GrapheneOS though.
@unaegeli @jonasgraphie @f @adfichter GrapheneOS is a privacy and security hardened OS greatly improving those compared to the Android Open Source Project. /e/ and iodéOS are not privacy or security hardened. Both reduce privacy and security compared to the Android Open Source Project. They both lag far behind on crucial standard privacy/security patches and don't fully ship them. They lack important standard protections. It's the opposite of GrapheneOS greatly improving patches and protections.
-
@unaegeli @jonasgraphie @f @adfichter GrapheneOS is a privacy and security hardened OS greatly improving those compared to the Android Open Source Project. /e/ and iodéOS are not privacy or security hardened. Both reduce privacy and security compared to the Android Open Source Project. They both lag far behind on crucial standard privacy/security patches and don't fully ship them. They lack important standard protections. It's the opposite of GrapheneOS greatly improving patches and protections.
@unaegeli @jonasgraphie @f @adfichter We take great care to preserve compatibility with our privacy and security features. Unfortunately, many apps have memory corruption bugs detected by improved memory protections so we provide toggles to work around it. Hardware memory tagging is mostly opt-in for user installed apps due to how many bugs it finds in them, but we recommend users enable the global toggle for it. Our dynamic code loading restrictions are similarly opt-in for user installed apps.
-
@unaegeli @jonasgraphie @f @adfichter We take great care to preserve compatibility with our privacy and security features. Unfortunately, many apps have memory corruption bugs detected by improved memory protections so we provide toggles to work around it. Hardware memory tagging is mostly opt-in for user installed apps due to how many bugs it finds in them, but we recommend users enable the global toggle for it. Our dynamic code loading restrictions are similarly opt-in for user installed apps.
@unaegeli @jonasgraphie @f @adfichter Banking and government apps have the unique issue of including misguided anti-tampering checks trying to detect a modified app or OS. It's an insecure approach and can be easily bypassed by attackers. These anti-tampering checks often wrongly detect added security protections as tampering. That's what's happening in this case. We have a way to work around it but it's not a per-app toggle since we didn't anticipate apps going out of the way to detect it.