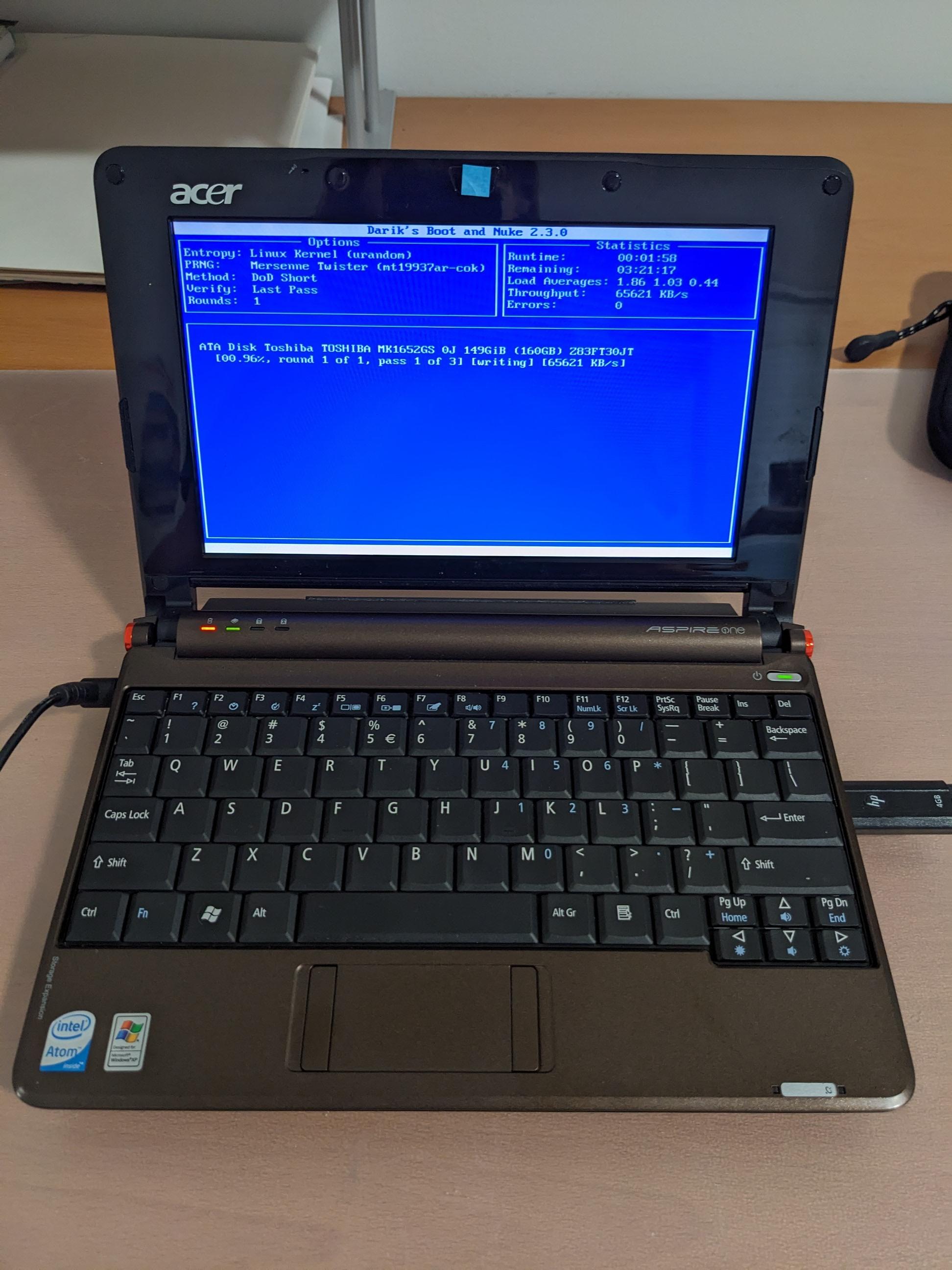
I've been physically destroying several old hard drives and prepping a pile of old electronics for recycling.
-
@zer0unplanned @Nonya_Bidniss @n_dimension there are tools like
shredthat do the repeat overwrites with random data, 0s & 1s.- Just iterate over your physical drives and you should be good
- That does work fine, and is kinda essential with shitty hosters [i.e. Hetzner] that tend to not even replace/delete the vHDD of their VPSes after customers cancel them.
@zer0unplanned @Nonya_Bidniss @n_dimension OFC physically destroying the drives among dozens if not hundreds of identical ones with a physical shredder is also an option, but neither cheap nor fast.
- But in many cases that is the mandated way to do things to ease off lawyers and in any decent organization CISO & CLO will approve of it if they didn't mandate it already…
- Just iterate over your physical drives and you should be good
-
@zer0unplanned @Nonya_Bidniss @n_dimension there are tools like
shredthat do the repeat overwrites with random data, 0s & 1s.- Just iterate over your physical drives and you should be good
- That does work fine, and is kinda essential with shitty hosters [i.e. Hetzner] that tend to not even replace/delete the vHDD of their VPSes after customers cancel them.
- Just iterate over your physical drives and you should be good
-
@zer0unplanned @Nonya_Bidniss @n_dimension OFC physically destroying the drives among dozens if not hundreds of identical ones with a physical shredder is also an option, but neither cheap nor fast.
- But in many cases that is the mandated way to do things to ease off lawyers and in any decent organization CISO & CLO will approve of it if they didn't mandate it already…
@kkarhan @n_dimension @Nonya_Bidniss No it is slow by design , I copied once the nuke OS of Kodachi OS which is Debian as the scripts are all viewable and copy pasta'able and made an usb with a universal script to nuke any machine once plugged in -
@kkarhan @n_dimension @Nonya_Bidniss No it is slow by design , I copied once the nuke OS of Kodachi OS which is Debian as the scripts are all viewable and copy pasta'able and made an usb with a universal script to nuke any machine once plugged in
@zer0unplanned @Nonya_Bidniss @n_dimension yeah, I do want to do something similar with @OS1337 but a bit more precise, aiming fir #LUKS headers first so it'll take literally seconds to make it already non-recoverable.
-
@zer0unplanned @Nonya_Bidniss @n_dimension yeah, I do want to do something similar with @OS1337 but a bit more precise, aiming fir #LUKS headers first so it'll take literally seconds to make it already non-recoverable.
@kkarhan @n_dimension @OS1337 @Nonya_Bidniss That is a harder nut, but if you realy want you can even beat up LUKS while I still ask why? that LUKS would be just a key to read overwritten data.
The aim is the data not the external defences. -
@kkarhan @n_dimension @OS1337 @Nonya_Bidniss That is a harder nut, but if you realy want you can even beat up LUKS while I still ask why? that LUKS would be just a key to read overwritten data.
The aim is the data not the external defences.@zer0unplanned @Nonya_Bidniss @n_dimension Mostly because deleting/overwriting the header first is extremely fast and twarts any unauthorized data recovery early on.
- This is a real security concern in #finance, where #ITsec literally has to deal with "Red Army Faction"-style hodtage taking scenarios as part of regulator-mandated #OpSec.
Just because a business doesn't have a shitton of cash at hand and banks neither doesn't mean that armed robbers would necessarily understand, much less accept.
- Similarly one may need to transit sensitive data but has to safeguard it against unauthorized access no matter the party accessing whilst providing plausible cooperation of it.
-
@zer0unplanned @Nonya_Bidniss @n_dimension Mostly because deleting/overwriting the header first is extremely fast and twarts any unauthorized data recovery early on.
- This is a real security concern in #finance, where #ITsec literally has to deal with "Red Army Faction"-style hodtage taking scenarios as part of regulator-mandated #OpSec.
Just because a business doesn't have a shitton of cash at hand and banks neither doesn't mean that armed robbers would necessarily understand, much less accept.
- Similarly one may need to transit sensitive data but has to safeguard it against unauthorized access no matter the party accessing whilst providing plausible cooperation of it.
@zer0unplanned @Nonya_Bidniss @n_dimension Either way, comitting "#AssetDenial" is more often than not necessary and one may only have a few seconds before those exercising force may realize that a "duress code" was used and going for the #LUKS headers first may be the only feasible option in a short time...
-
@zer0unplanned @Nonya_Bidniss @n_dimension Either way, comitting "#AssetDenial" is more often than not necessary and one may only have a few seconds before those exercising force may realize that a "duress code" was used and going for the #LUKS headers first may be the only feasible option in a short time...
@kkarhan @n_dimension @Nonya_Bidniss I'll try to do the same on an atomic image of fedora 43 as a pawn image in a box and will tell you if it worked with results. But need a 2nd fedora Atomic SilverBlue on that as a real challenge.
The years of me using Kali was very long ago just after backtrack, then I used Parrot OS rather but that all does not mater as it is all Debian RHEL
My os is immuatble with a rollback option> makes it very much trickier -
@n_dimension @kkarhan @Nonya_Bidniss there are scripts that nuke the whole OS and Kernel and DD, just 1 script to run on the pc .
Mr Robot used the chip for a microwave and pierced a hole in the HDD, in the movie whoami they used acid indeed with a mask on.
But just 1 script and you can overwrite the hdd or SDD or/and nuke the whole OS> I wish them good luck with that recovering anything.@zer0unplanned @kkarhan @Nonya_Bidniss
Problem with SSD "overwrite" is SSDs balance the writes.
So if your file is in A D J, SSD MAY balance the write to B E K to balance the cells.On the upside, SSD has one addressable cell, not a fuzzy magnetic dust.
-
@zer0unplanned @kkarhan @Nonya_Bidniss
Problem with SSD "overwrite" is SSDs balance the writes.
So if your file is in A D J, SSD MAY balance the write to B E K to balance the cells.On the upside, SSD has one addressable cell, not a fuzzy magnetic dust.