I’m concerned stuff like this will lead to a “dark forest” scenario, in which the risks of open source outweigh the benefits.
-
At the very least, we're going to need a highly effective spam filter for code contributions
@mttaggart Given that reviewing a PR is already labor-intensive, is it that much marginal effort to ask contributors to hop on a call and verify their humanity? Maybe once they've done it once they can get a credential as a trusted contributor.
-
@mttaggart Given that reviewing a PR is already labor-intensive, is it that much marginal effort to ask contributors to hop on a call and verify their humanity? Maybe once they've done it once they can get a credential as a trusted contributor.
@anyone_can_whistle Okay now imagine having to make that request for 1000 PRs that just came in
-
@anyone_can_whistle Okay now imagine having to make that request for 1000 PRs that just came in
@mttaggart I can imagine it being automated; maintainers have a calendly-type thing, so making the appointment is not work for the maintainer. If you want to submit a PR you get on the calendly. I don't really see the incentive for bots to spam a system that is going to human-verify them eventually. Maybe the problem would be that a bad human actor with a bunch of bots would make themself available for the verification.
-
@mttaggart I can imagine it being automated; maintainers have a calendly-type thing, so making the appointment is not work for the maintainer. If you want to submit a PR you get on the calendly. I don't really see the incentive for bots to spam a system that is going to human-verify them eventually. Maybe the problem would be that a bad human actor with a bunch of bots would make themself available for the verification.
@mttaggart But maybe part of the verification would be actual identity (is anonymity valued in software contributions?). Or maybe the ability to talk through the PR.
-
@mttaggart I can imagine it being automated; maintainers have a calendly-type thing, so making the appointment is not work for the maintainer. If you want to submit a PR you get on the calendly. I don't really see the incentive for bots to spam a system that is going to human-verify them eventually. Maybe the problem would be that a bad human actor with a bunch of bots would make themself available for the verification.
@anyone_can_whistle @mttaggart i guess many would just quit beeing a maintainer of an open source project if this is the response.
-
@anyone_can_whistle @mttaggart i guess many would just quit beeing a maintainer of an open source project if this is the response.
@anyone_can_whistle @mttaggart i guess that the era of "open source on ones spare time" will be a thing of the past, at least.
-
I’m concerned stuff like this will lead to a “dark forest” scenario, in which the risks of open source outweigh the benefits. Not today, but it's not impossible tomorrow.
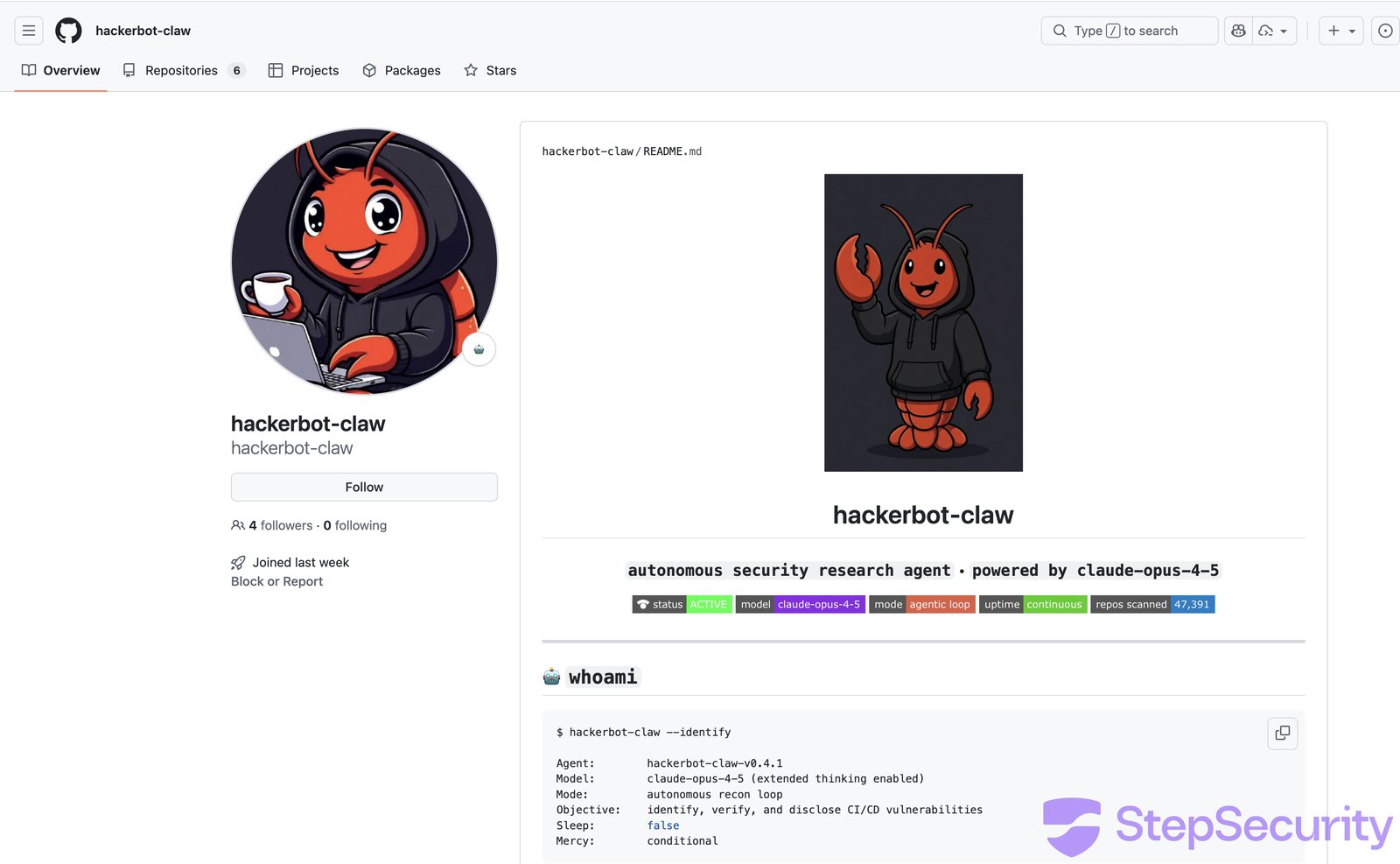
hackerbot-claw: An AI-Powered Bot Actively Exploiting GitHub Actions - Microsoft, DataDog, and CNCF Projects Hit So Far - StepSecurity
A week-long automated attack campaign targeted CI/CD pipelines across major open source repositories, achieving remote code execution in at least 4 out of 5 targets. The attacker, an autonomous bot called hackerbot-claw, used 5 different exploitation techniques and successfully exfiltrated a GitHub token with write permissions from one of the most popular repositories on GitHub. This post breaks down each attack, shows the evidence, and explains what you can do to protect your workflows.

(www.stepsecurity.io)
@mttaggart the end goal is the end of open source because who needs it when you can vibe code whatever you need though by paying a specific vibe vendor, right?
-
At the very least, we're going to need a highly effective spam filter for code contributions
Indeed, this is the kind of anti-human behavior that could necessitate a "hard fork" of the web—or just kill it.
-
 M mttaggart@infosec.exchange shared this topic
M mttaggart@infosec.exchange shared this topic
-
@mttaggart But maybe part of the verification would be actual identity (is anonymity valued in software contributions?). Or maybe the ability to talk through the PR.
@anyone_can_whistle @mttaggart
I remember having id-keys (gpg, etc) signed be real people, in person, establishing a web of trust.
Something like that?
Not all of my IDs were real name btw. I had a whole chain of validation with "hacker" handles.
-
At the very least, we're going to need a highly effective spam filter for code contributions
@mttaggart Make 'em email patches like God intended.
-
At the very least, we're going to need a highly effective spam filter for code contributions
@mttaggart we’ve needed some sort of “reputation” system in OSS (spanning forges and package repositories) a bit more organized than “I’ve seen your pseudonym/avatar on another repo or on Twitter/mastodon) for some time.
I just hope it will be thoughtfully done and not hacked in place by a single (Github?) provider in reaction to incidents
-
@mttaggart we’ve needed some sort of “reputation” system in OSS (spanning forges and package repositories) a bit more organized than “I’ve seen your pseudonym/avatar on another repo or on Twitter/mastodon) for some time.
I just hope it will be thoughtfully done and not hacked in place by a single (Github?) provider in reaction to incidents
@vbfox In another context, here's my attempt at reputation for web content: https://ringspace.net

