Hi folks.
-
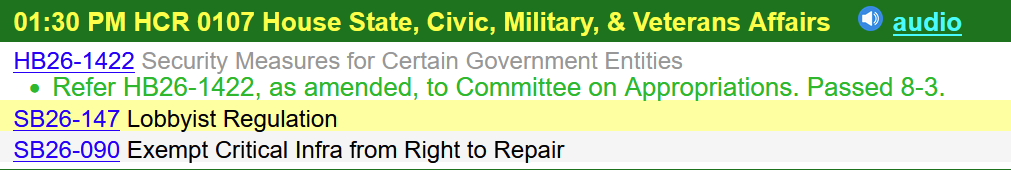
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
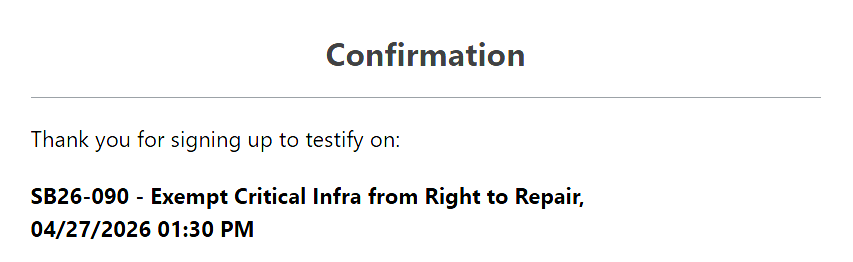
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch I’m going to try to make it in person. Not in info sec, but am Electrical and sw eng.
-
@threatresearch I’m going to try to make it in person. Not in info sec, but am Electrical and sw eng.
Thank you!
I appreciate the short notice on this presents a problem for many.
Unfortunately, the way the legislature works, we often don't hear about these scheduled hearings until the day of.
But written testimony is also an option if you can't make it to the hearing during its scheduled time.
-
R relay@relay.publicsquare.global shared this topic
-
Thank you!
I appreciate the short notice on this presents a problem for many.
Unfortunately, the way the legislature works, we often don't hear about these scheduled hearings until the day of.
But written testimony is also an option if you can't make it to the hearing during its scheduled time.
@threatresearch I live pretty close and have the luxury of a flexible schedule. Plus, my only meeting today already happened.
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch I'm so glad you tooted about this. I submitted written testimony just now, hopefully they will be flooded and strike this bill down. The right to repair needs to be protected by our legislature since it is not protected by our Constitution. I wish it was amended into there though...one day it will be!
-
@threatresearch I'm so glad you tooted about this. I submitted written testimony just now, hopefully they will be flooded and strike this bill down. The right to repair needs to be protected by our legislature since it is not protected by our Constitution. I wish it was amended into there though...one day it will be!
@JDGeoShack Thank you!

-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch Done!
I probably should have done written testimony, but I'm feeling spicy.
-
@threatresearch Done!
I probably should have done written testimony, but I'm feeling spicy.
-
@threatresearch Done!
I probably should have done written testimony, but I'm feeling spicy.
@NosirrahSec spicy is good. Remember that the committee is not acting out of malice, but is ignorant of these principles. Treat them as you would an errant child who is making a mistake.
-
@NosirrahSec spicy is good. Remember that the committee is not acting out of malice, but is ignorant of these principles. Treat them as you would an errant child who is making a mistake.
@threatresearch I figure as much, as as volatile as I am out here, I'm treating this as a professional engagement. (obviously)
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch colorado was once part of the USA.
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch written comments submitted.
-
@threatresearch written comments submitted.
@colo_lee Thanks, Lee!

-
@colo_lee Thanks, Lee!

@threatresearch and thank you for alerting us!
-
@threatresearch I live pretty close and have the luxury of a flexible schedule. Plus, my only meeting today already happened.
@threatresearch So glad I got here early. Almost 2 and there's no committee here yet. At least 3 of us IT types and at least one lobbyist in the hallway
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
@threatresearch They did update the bill having the AG be the one to determine what is and is not "critical infrastructure" I suppose that's a small improvement, but I'm not holding my breath.
hearing started a few min ago, but there are two other bills first.
-
Hi folks. It's Andrew with another update on our battle over the "wrong to repair" bill that continues to move through the Colorado legislature, SB26-090.
I am asking anyone, but especially those with a background as a cybersecurity practitioner, to please consider submitting written or live/virtual testimony TODAY to the committee who will be hearing this bill, starting at 1:30pm mountain time.
This afternoon, in a little under four hours, a House committee will be hearing testimony on the bill. If you have been waiting for your moment, this might be the last chance you have this session to weigh in and express your support for this critical right we may lose in the next few days.
Opponents of Colorado's right to repair law, which only came into effect on January 1, include companies like IBM and Cisco Systems. They are making outrageous and counterfactual claims about the right to repair in order to pressure lawmakers into accepting this bill that would exclude any technology classified as "critical infrastructure" as exempt from the right to repair law.
One of the most egregiously wrong claims they have repeatedly made is that a "right to repair" items like a firewall somehow makes the products Cisco and IBM sell less safe from a cybersecurity perspective. After the committee hearing last month, I spoke in the hallway with the government affairs person from Cisco. I asked him to explain it to me, a cybersecurity professional, why being able to fix a broken firewall presents a cybersecurity risk.
He could not explain it, simply repeating that giving people access to internal schematics in order to let them repair parts in a network edge device somehow presents a risk that adversaries would then be able to more easily reverse-engineer the product.
The cybersecurity folks know where this is leading: They are claiming that the obscurity of their documentation about their products is the cybersecurity feature that protects them from attack.
Those of us who are practitioners in this space know that obscurity provides no security whatsoever in the long term, and that giving people the ability to replace broken parts, like power supplies, does not threaten the cybersecurity of a router or firewall any more than replacing a power cord.
After all, data centers have tight security about who is allowed in or out, and engage with cyber- and physical pentesters to routinely check the security of their facilities.
The reality is that the west's biggest adversary, China, already has every model of every firewall on earth in its possession, and has thrown brigades of bodies at them to perform the reverse engineering Cisco claims they want to prevent. That cat is out of the bag. This bill will not provide any cybersecurity protection to any Cisco firewall.
As I said to the Cisco lobbyist, if an adversary already has physical access to the device, it's game over. Adversaries don't swap out broken hard drives or power supplies.
Beyond that specious argument, there is a secondary problem with the bill: It never defines with any necessary level of detail what comprises "critical infrastructure" - which means that, if a regular, commercial TV set you can buy at Costco is being used as a monitor in a SOC, it's possible that those commercial products will end up lumped into the category of "critical infrastructure."
We all know that what makes electronic infrastructure critical is not what it is - phones, laptops, desktops, printers, scanners, even desk lamps - but how and where, and for what purpose it is used
What this bill appears to be about, and why Cisco and IBM are fighting to advance it so hard, is that it enables the rent-seeking behavior of companies who want to lock their customers in to expensive annual support contracts, and lock third-party support companies out of the equation. That's literally all this is, a way to defend an ongoing revenue stream. Any arguments other than that make no sense.
If you can, please consider testifying in person: The lobbyists have seemingly infinite time and access to these legislators, and have been steamrolling the entire process through, using ridiculous lies and arguments that make no sense to anyone with background as a practitioner.
we want to focus on three core messages:
This bill is ridiculously broad and would sweep up most IT equipment, limiting repair options for everyone from Fortune 500 companies to small mom-and-pop businesses, schools, hospitals, libraries, universities, local governments, law enforcement agencies and more.
It is a false premise to claim that repair tools are a security risk and limiting those tools to the manufacturer's repairers is safer.
This bill allows manufacturers to lock out repair competition and monopolize repair for their products
that drives up costs, reduces quality and can undermine the secondary market.
If you can share your personal background and experience and speak to how limiting access to repair tools will not make products safer would be great. You don't need to be a Colorado resident, or even based in the US.
Here's how you do it:
sign up to testify here: https://sites.coleg.gov/public-testimony/sign-up-to-testify/step-1- Search for SB26-090
- Select the bill when it pops up
- Fill in your details including whether you are testifying in-person or remotely. Please select "Oppose" for your position.
- Enter your information
- Show up and, when called, give your two (or three, depending on how many/few sign up) minutes of testimony, and be prepared to answer questions
The people pushing this bill are counting on the fact that this is happening in the middle of a workday, when we're all trying to wreck hackers. But this is a case where we, as a community, need to stand up for what's right. Not doing so will make all of our jobs harder in the future. I hope to see you there.
#COpolitics #RightToRepair #activism #hackers #cybersecurity #cybersicherheit #cyberseguridad
A quick update: The SB26-090 hearing is scheduled last on today's agenda for the committee it is in. It could be hours before it begins. You can monitor the topics the committee is looking into on this website:
https://www.leg.state.co.us/public/display.nsf/index.html
(Be sure to click HOU Cmtes then scroll to the bottom to find it)
There is a live stream of the hearing here: https://sg001-harmony.sliq.net/00327/Harmony/en/PowerBrowser/PowerBrowserV2/20260427/33/18751
-
@threatresearch They did update the bill having the AG be the one to determine what is and is not "critical infrastructure" I suppose that's a small improvement, but I'm not holding my breath.
hearing started a few min ago, but there are two other bills first.
@johne It's really not any change at all, because it isn't the "thing" that is critical infra, but how the organization uses the thing. How can an AG make that kind of determination on the millions of devices used by thousands of companies, agencies, local governments, etc.? It's a ludicrous conceit - the AG office is busy prosecuting major cases, and doesn't have time for this - and would require staffing and funding that, under the current budget, simply doesn't exist.
-
@johne thank you for sticking it out.
-
A quick update: The SB26-090 hearing is scheduled last on today's agenda for the committee it is in. It could be hours before it begins. You can monitor the topics the committee is looking into on this website:
https://www.leg.state.co.us/public/display.nsf/index.html
(Be sure to click HOU Cmtes then scroll to the bottom to find it)
There is a live stream of the hearing here: https://sg001-harmony.sliq.net/00327/Harmony/en/PowerBrowser/PowerBrowserV2/20260427/33/18751
SB26-090 update: The committee has finished with the first item and moved on to the second item in their agenda. The 090 hearing comes after this one about lobbyists